
Discovering Tunneling Service Security Flaws in AnyDesk Remote Application
Anydesk is a remote desktop application that has amassed popularity and market share in recent years with the growing adoption of remote work models.
During routine work with Anydesk, Argus’ research team stumbled upon & reported two security flaws (aka CVEs) that could possibly impact users.
This post describes both security issues and their potential impact on anyone using the AnyDesk tunneling service.
CVE-2021-44425: Tunneling socket unnecessarily binds to default route
The Issue
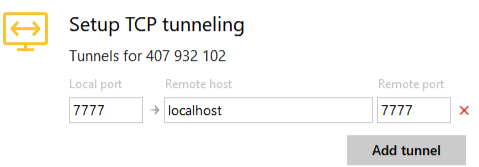
The issue pertains to configuring a TCP tunnel to a remote AnyDesk device, e.g.:
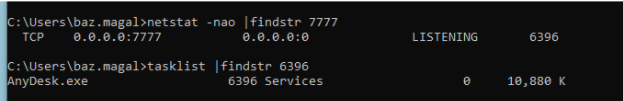
The AnyDesk software on the connecting client listens for connections to the tunnel on all interfaces:
The Threat
Let’s assume a corporate worker uses the Anydesk tunneling feature to connect to a remote server within his organizational network and proceeds to interact with an internal service using the tunneled port.
If he does so while connecting to a non-secure network (e.g., he is connected to a café hotspot), an attacker connected to the same café hotspot would have direct access to the corporate remote server via the exposed tunneled port. The attacker would potentially be able to compromise the service listening to the port, and possibly advance further within the “secure” corporate network and access sensitive data. Additionally, the attacker would have access to the Anydesk tunneling communication stack of the corporate worker.
CVE-2021-44426: A malicious file can be planted in an unsuspecting victim’s computer
The Issue
Let’s assume two people are connected to the same remote Anydesk session. Under certain circumstances, if Person A copies a file from the remote computer to his/her local machine, the same file will be copied to Person B’s local machine (to the ~/Downloads/<timestamp>/ directory) without any prompt or approval from Person B.
The Threat
Assume an attacker opens an Anydesk session connecting to a remote computer that contains a malicious file. If an attacker can persuade an innocent victim to connect to the same remote computer, the attacker can plant the malicious file in the victim’s filesystem without the knowledge of the victim. Such malware could be used in a subsequent attack to compromise the victim’s computer.
Responsible Disclosure Timeline
The Argus Cyber Security Research team reported both issues to Anydesk, who verified their validity and then fixed them according to the following timeline:
August 2021 – Issues were discovered and verified on relevant versions
September 9, 2021 – Issues were reported to Anydesk
September 22, 2021 – Anydesk informed Argus that both issues were verified by their security team
November 9, 2021 – Anydesk informed Argus that both issues were fixed on all relevant software versions.
November 29, 2021 – CVE ID Request regarding both issues was submitted to MITRE






