- 製品
- サービス
- ソリューション
- ソリューション
- Argus Small-Series Starter kit
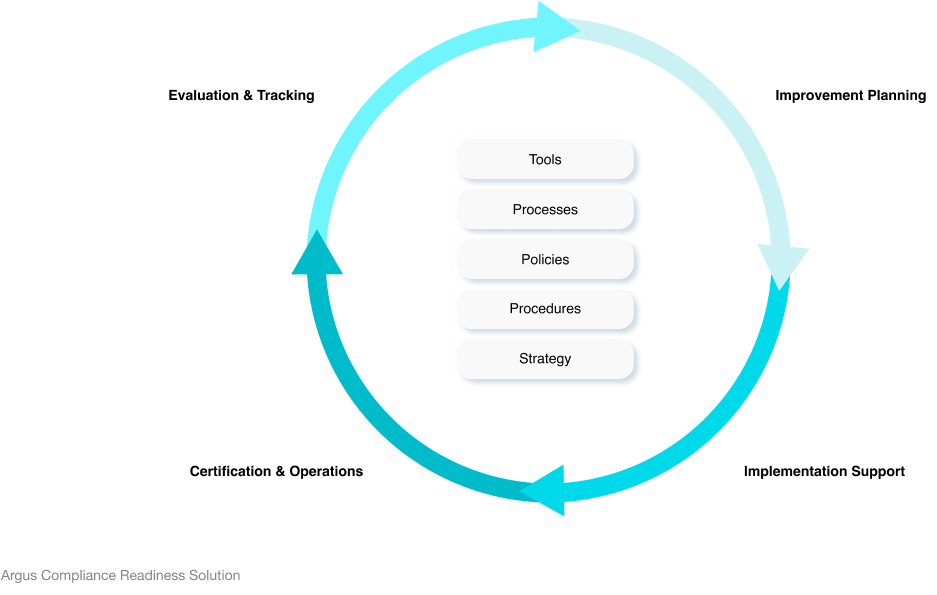
少量生産を行うOEMおよび部品サプライヤーの コンプライアンス対応ソリューション
- Argus Fraud Detection
ソフトウエア デファインド ビークルにおける不正行為を特定し、財務リスクと風評リスクを低減します。
- Argus Ethernet Switch Protection
車載イーサネットスイッチによる サイバーセキュリティ保護
- Argus In-Vehicle Infotainment Cyber Guard
車載インフォテインメント向けの高度なサイバーセキュリティ
- Argus Zone Control Unit Protection
車両ゾーンコントロールユニットのサイバーセキュリティ
- リソース
- 企業情報